Identify the most impactful security improvements to reduce risk and enable business initiatives
Level up your security planning.
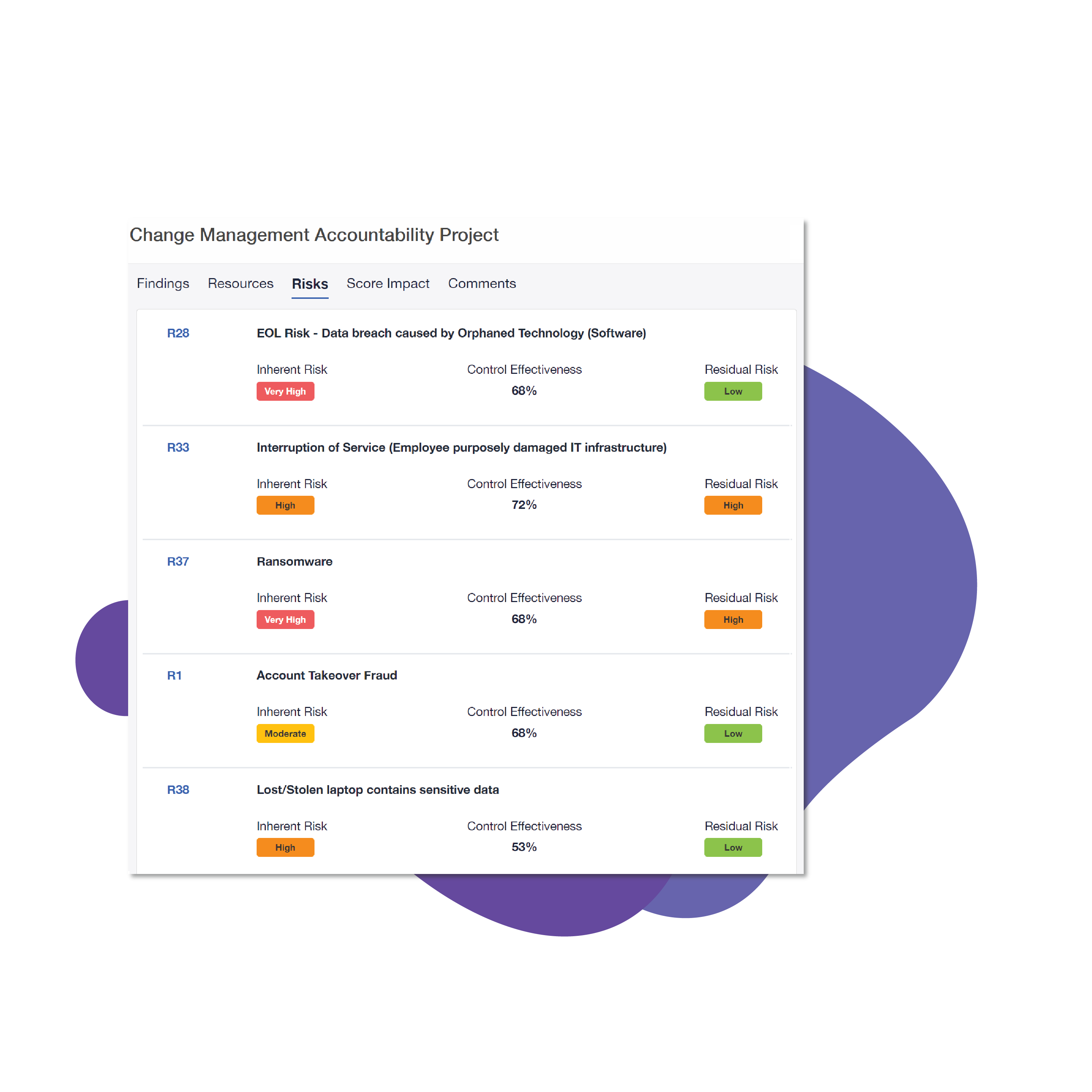
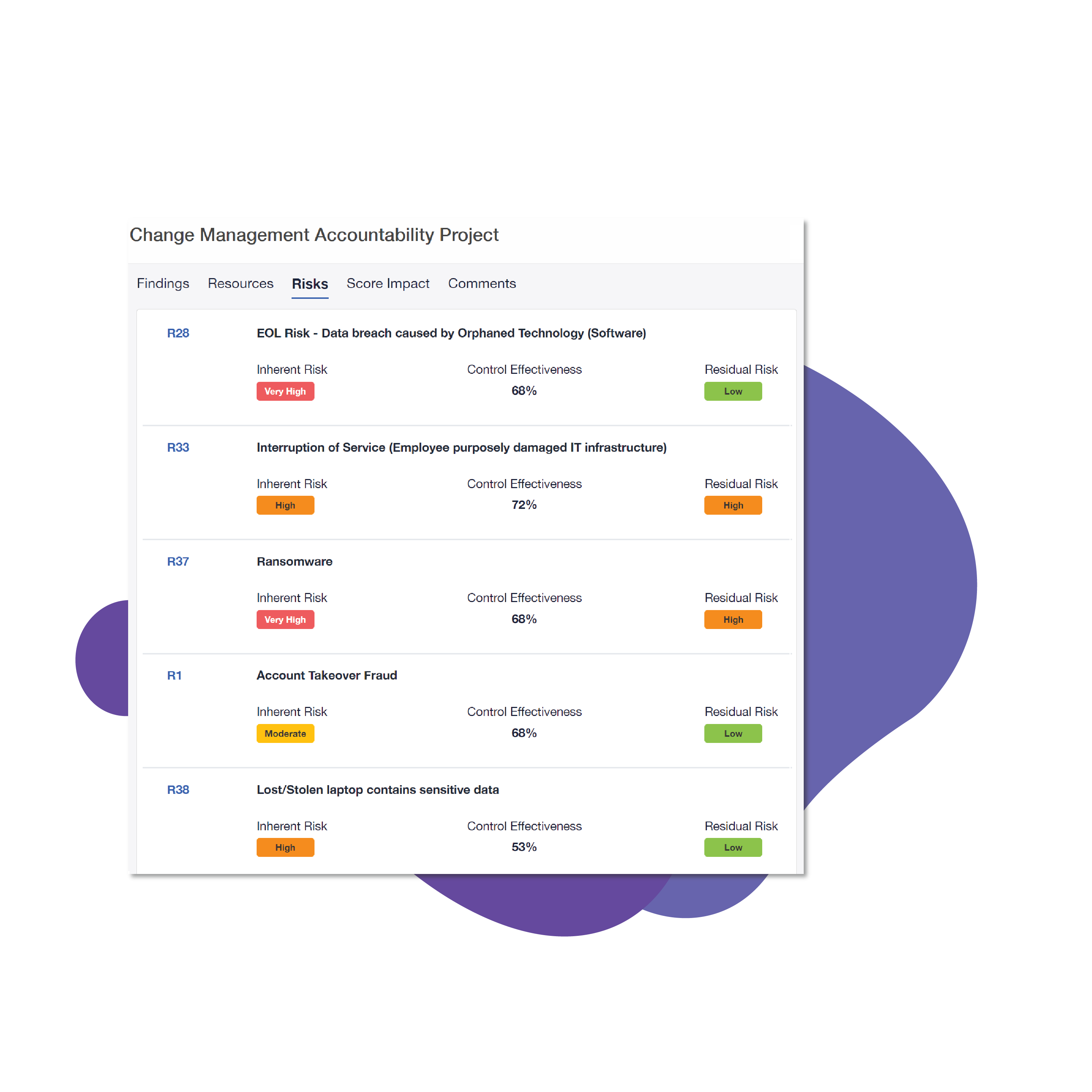
Blue Lava arms you with a comprehensive understanding of the current state of your security program. By tying findings and security gaps to common risks, you can confidently prioritize projects and investments that carry the biggest impact to the business.
Feature Overview
Blue Lava Smart Priorities
Simulate and Compare
Compare program maturity scenarios for data-driven decision-making to justify budget needs
Projects
See how your plan will impact your security program based on security maturity and risk
Jira Integration
Sync program improvements seamlessly with Jira tickets for easy two-way project management
Use Cases

Take Action
Leverage suggested prioritization and recommended remediation steps
Evaluate Investments
Identify areas of potential over-and under-investment, aligning the security program to your organization’s risk profile
Elevate the Discussion
Change the conversation from technical risks to strategic business alignment
Manage Projects
Skip the spreadsheets and manage your program growth in one centralized location, including Jira ticketing integration
Related resources
Achieving Security Program Maturity
Ensuring your security program is defined, aligned, and implemented to have the greatest impact on the business.


The Urgency to Treat Cybersecurity as a Business Decision
One of the most critical elements of the CISO role is the ability to communicate your security program needs to your executive team and the board.
Examining the CISO Role: Achieving Maturity Through Transparency and Consistency
Alignment between business and information security improves with maturity: what’s the impact and which “side” needs to “mature?”